Cisco 300-720 - Securing Email with Cisco Email Security Appliance (300-720 SESA)
An engineer must share threat reporting information from Cisco Secure Email Gateway to Cisco SecureX. Which setting must be enabled in Secure Email Gateway?
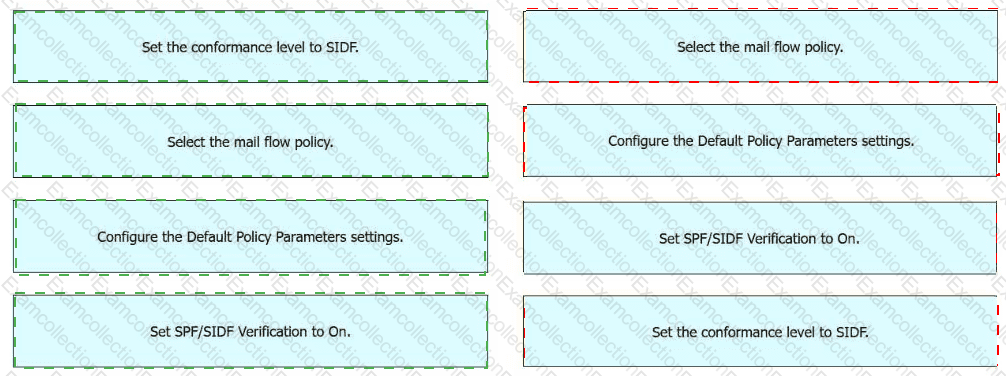
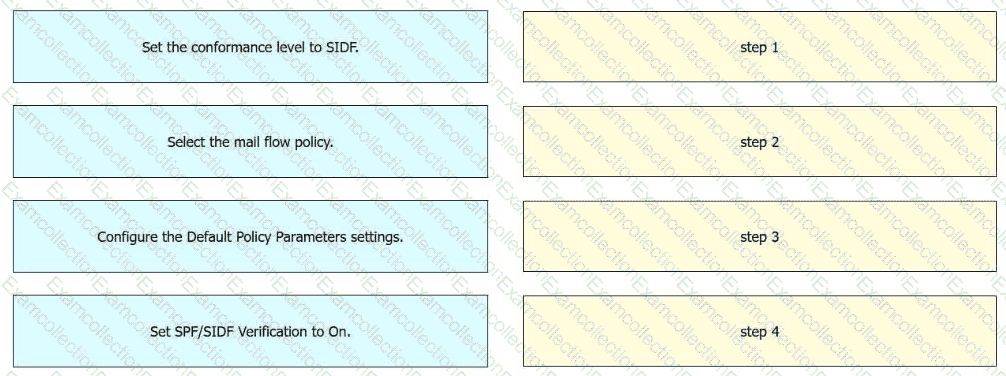
An engineer must enable SIDF for a mail flow policy on an incoming listener in Cisco Secure Email Gateway. Drag and drop the actions from the left into the sequence on the right to meet the requirement.
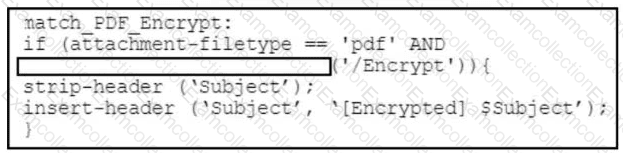
Refer to the exhibit. A security engineer must create a message filter on a Cisco Secure Email Gateway to scan all incoming emails for encrypted PDF files. Which code snippet completes the message filter?
What is a benefit of graymail services?
Which method enables an engineer to deliver a flagged message to a specific virtual gateway address in the most flexible way?
Which type of query must be configured when setting up the Spam Quarantine while merging notifications?
What is needed to sign outbound emails using Domain Keys Identified Mail after a signing profile is created in the Cisco Secure Email Gateway?
An engineer is configuring a Cisco ESA for the first time and needs to ensure that any email traffic coming from the internal SMTP servers is relayed out through the Cisco ESA and is tied to the Outgoing Mail Policies.
Which Mail Flow Policy setting should be modified to accomplish this goal?
Which feature must be configured before an administrator can use the outbreak filter for nonviral threats?
Which content filter condition checks to see if the " From: header " in the message is similar to any of the users in the content dictionary?