Cisco 300-720 - Securing Email with Cisco Email Security Appliance (300-720 SESA)
An engineer is testing mail flow on a new Cisco ESA and notices that messages for domain abc.com are stuck in the delivery queue. Upon further investigation, the engineer notices that the messages pending delivery are destined for 192.168.1.11, when they should instead be routed to 192.168.1.10.
What configuration change needed to address this issue?
Which Cisco Secure Email Threat Defense visibility and remediation mode is only available when using Cisco Secure Email Gateway as the message source?
An email containing a URL passes through the Cisco ESA that has content filtering disabled for all mail policies. The sender is sampleuser@test1.com, the recipients are testuser1@test2.com, testuser2@test2.com, testuser3@test2.com, and mailer1@te st2.com. The subject of the email is Test Document395898847. An administrator wants to add a policy to ensure that the Cisco ESA evaluates the web reputation score before permitting this email.
Which two criteria must be used by the administrator to achie ve this? (Choose two.)
What occurs when configuring separate incoming mail policies?
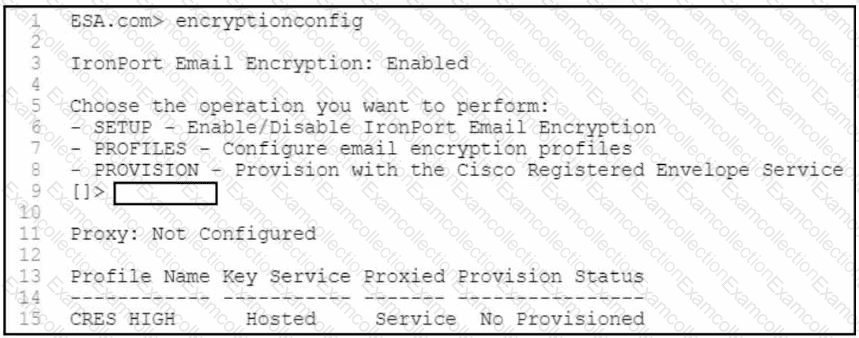
Refer to the exhibit. A security engineer must configure a Cisco Secure Email Gateway to ensure that encryption is enabled and the configured profile is provisioned. Which command must be used?
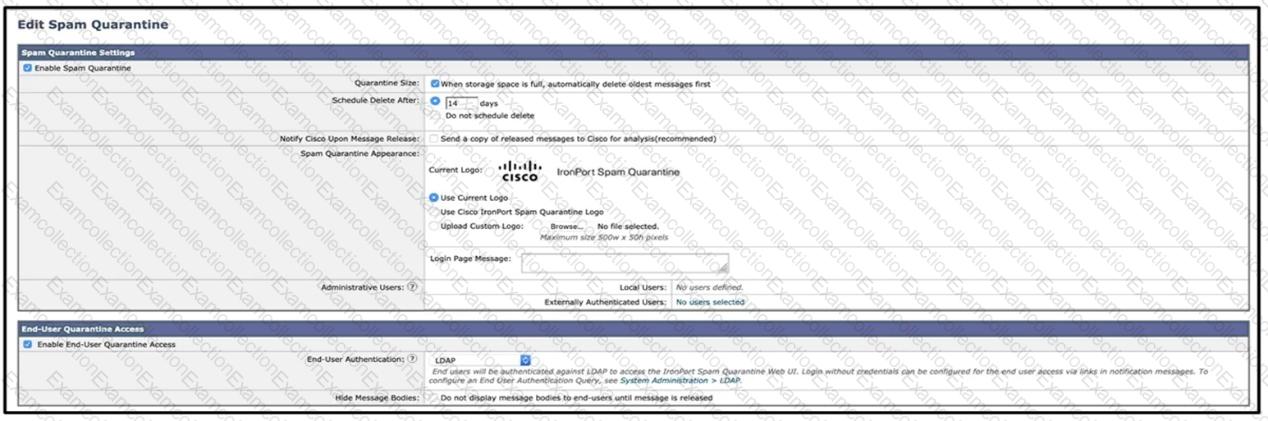
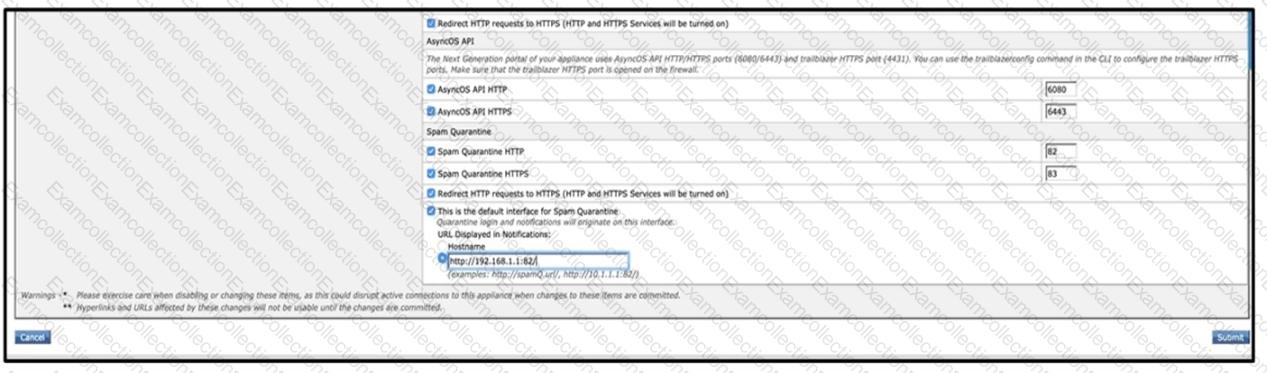
Refer to the exhibits. What must be done to enforce end user authentication before accessing quarantine?
Which of the following two statements are correct about the large file attachments (greater than 25MB) feature in Cisco Secure Email Encryption Service? (Choose two.)
Which two statements about configuring message filters within the Cisco ESA are true? (Choose two.)
Which two steps configure Forged Email Detection? (Choose two.)
What are two primary components of content filters? (Choose two.)



