Cisco 300-740 - Designing and Implementing Secure Cloud Access for Users and Endpoints (SCAZT)
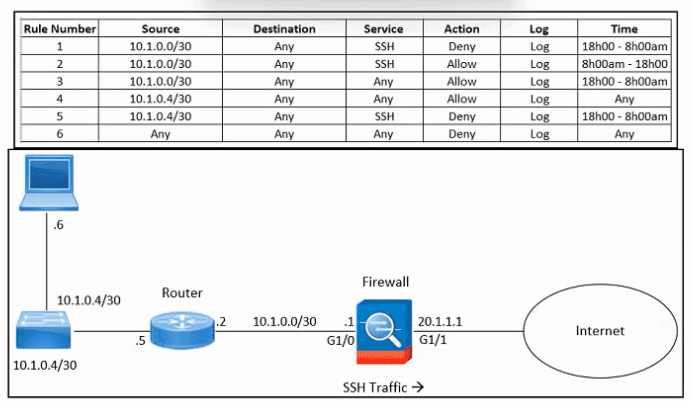
Refer to the exhibit. An engineer must troubleshoot an issue with excessive SSH traffic leaving the internal network between the hours of 18:00 and 08:00. The engineer applies a policy to the Cisco ASA firewall to block outbound SSH during the indicated hours; however, the issue persists. What should be done to meet the requirement?
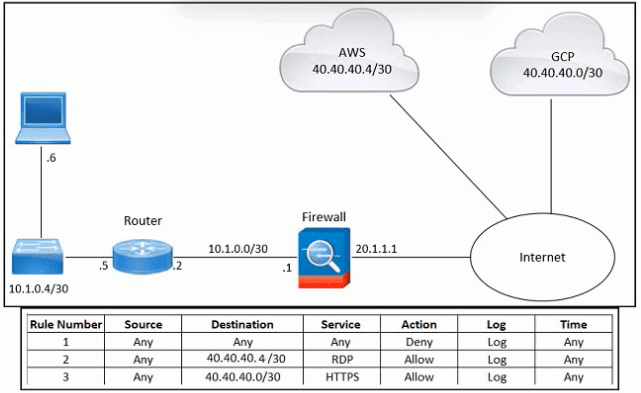
Refer to the exhibit. An engineer must provide RDP access to the AWS virtual machines and HTTPS access to the Google Cloud Platform virtual machines. All other connectivity must be blocked. The indicated rules were applied to the firewall; however, none of the virtual machines in AWS and Google Cloud Platform are accessible. What should be done to meet the requirement?
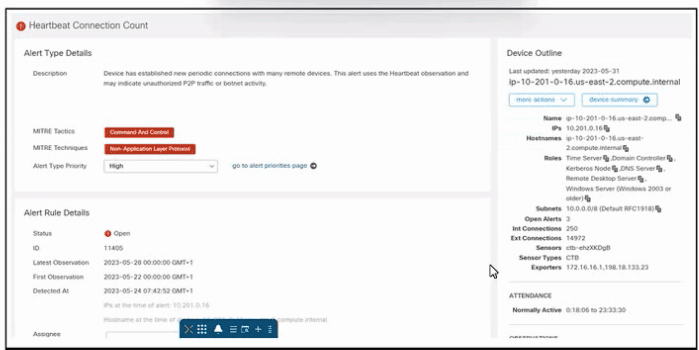
Refer to the exhibit. An engineer is investigating an unauthorized connection issue using Cisco Secure Cloud Analytics. Which two actions must be taken? (Choose two.)
What does the Cisco Telemetry Broker provide for telemetry data?
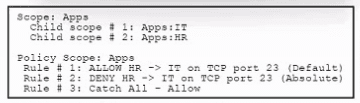
Refer to the exhibit. An engineer must analyze a segmentation policy in Cisco Secure Workload. What is the result of applying the policy?
Which concept is used in the Cisco SAFE key reference model?
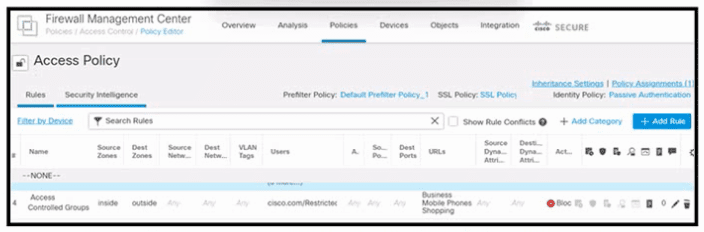
Refer to the exhibit. An engineer must create a policy in Cisco Secure Firewall Management Center to prevent restricted users from being able to browse any business or mobile phone shopping websites. The indicated policy was applied; however, the restricted users still can browse on the mobile phone shopping websites during business hours. What should be done to meet the requirement?
In the zero-trust network access model, which criteria is used for continuous verification to modify trust levels?
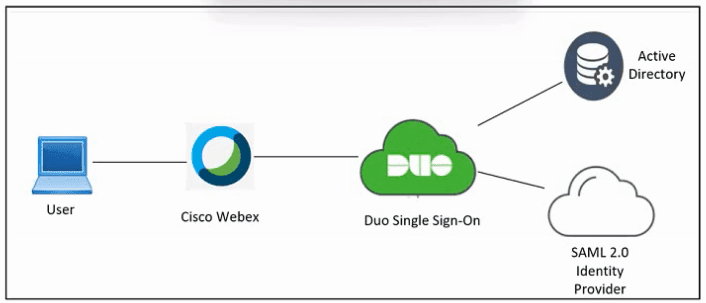
Refer to the exhibit. An engineer must configure Duo SSO for Cisco Webex and add the Webex application to the Duo Access Gateway. Which two actions must be taken in Duo? (Choose two.)
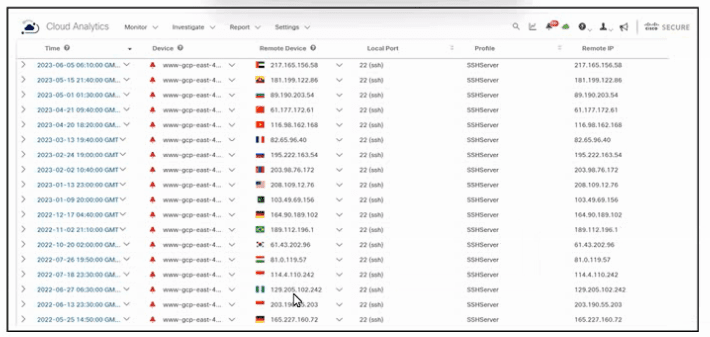
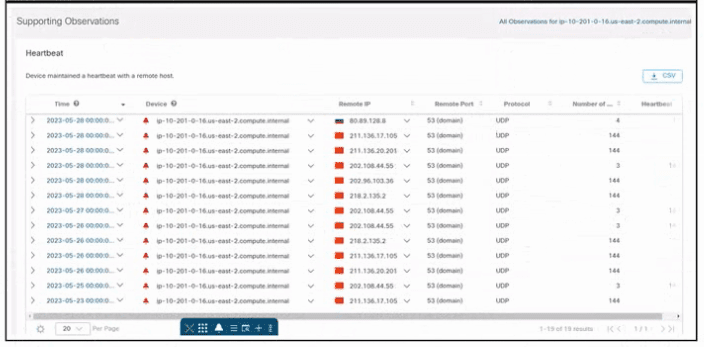
Refer to the exhibit. An engineer must analyze the Cisco Secure Cloud Analytics report. What is occurring?



