ECCouncil 312-96 - Certified Application Security Engineer (CASE) JAVA
Which of the following is used to mapCustom Exceptions to Statuscode?
Which of the following relationship is used to describe security use case scenario?
It is recommended that you should not use return, break, continue or throw statements in _________
In a certain website, a secure login feature is designed to prevent brute-force attack by implementing account lockout mechanism. The account will automatically be locked after five failed attempts. This feature will not allow the users to login to the website until their account is unlocked. However, there is a possibility that this security feature can be abused to perform __________ attack.
Which of the following can be derived from abuse cases to elicit security requirements for software system?
Alice works as a Java developer in Fygo software Services Ltd. He is given the responsibility to design a bookstore website for one of their clients. This website is supposed to store articles in .pdf format. Alice is advised by his superior to design ArticlesList.jsp page in such a way that it should display a list of all the articles in one page and should send a selected filename as a query string to redirect users to articledetails.jsp page.
Alice wrote the following code on page load to read the file name.
String myfilename = request.getParameter("filename");
String txtFileNameVariable = myfilename;
String locationVariable = request.getServletContext().getRealPath("/");
String PathVariable = "";
PathVariable = locationVariable + txtFileNameVariable;
BufferedInputStream bufferedInputStream = null;
Path filepath = Paths.get(PathVariable);
After reviewing this code, his superior pointed out the security mistake in the code and instructed him not repeat the same in future. Can you point the type of vulnerability that may exist in the above code?
Which of the following relationship is used to describe abuse case scenarios?
Which of the following method will help you check if DEBUG level is enabled?
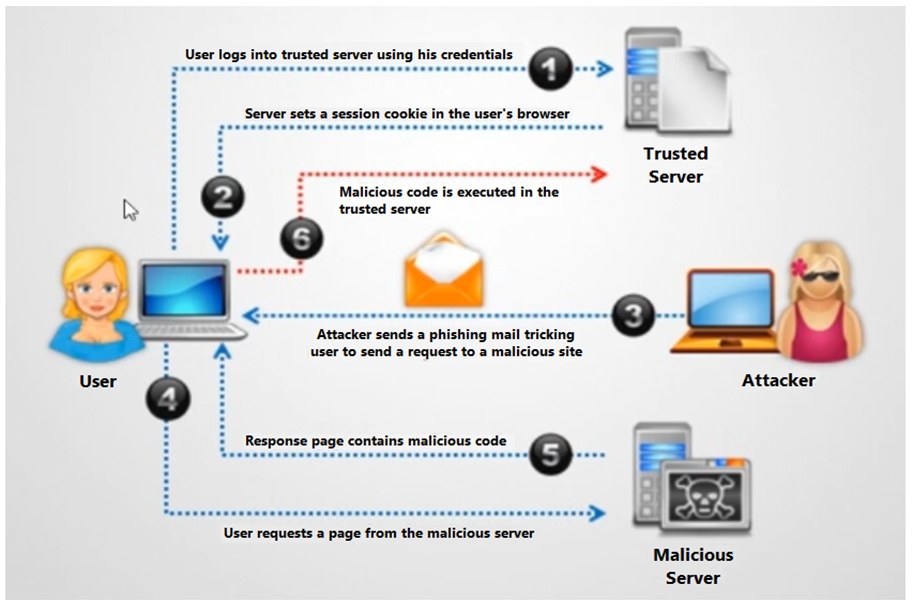
Identify the type of attack depicted in the figure below:
Identify the formula for calculating the risk during threat modeling.



