Cisco 350-401 - Implementing Cisco Enterprise Network Core Technologies (350-401 ENCOR)
Which definition describes JWT in regard to REST API security?
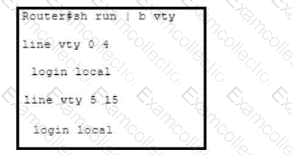
Refer to the exhibit. The existing configuration must be updated to terminate all EXEC sessions after 120 minutes. Which command set should be applied?
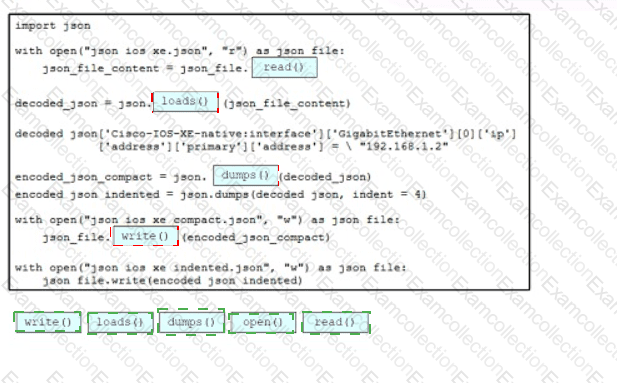
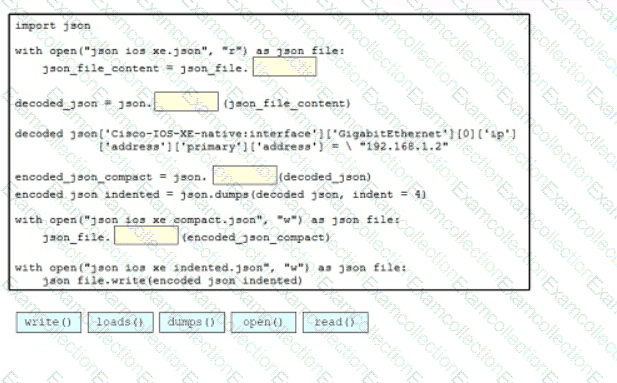
Drag and drop the code snippets from the bottom onto blanks m the Python script so that the program changes the IP address and saves It as a new JSON Me on the disk Not all options are used
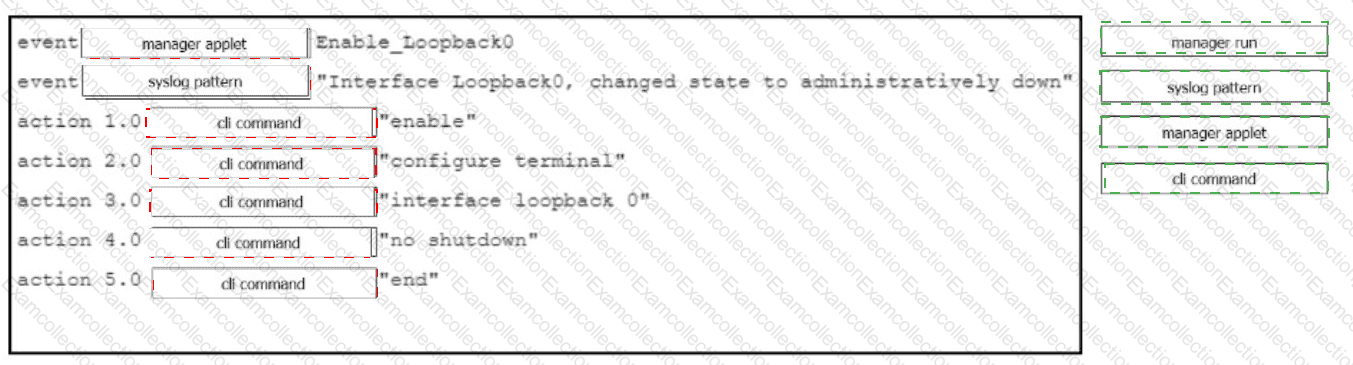
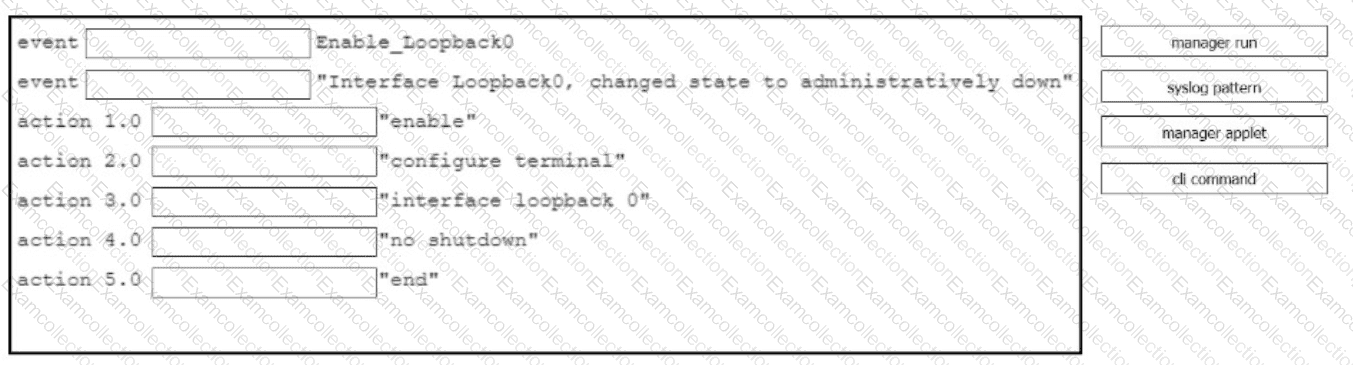
Drag and drop the command snippets from the right onto the boxes to create an EEM applet that will enable interface LoopbackO when the logging message ' Interface LoopbackO. changed state to administratively down " is received. Not all commands are used and some commands are used more than once.
When using a Cisco Catalyst 9800 Series WLC, which tag/profile can be applied to APs to change the mode to FlexConnect in a specific location?
Which characteristic applies to a traditional WAN solution but not to a Cisco Catalyst SD-WAN solution?
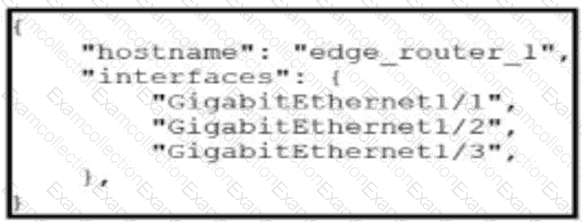
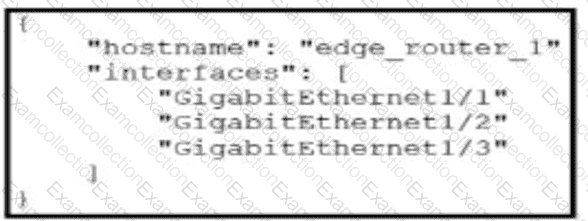
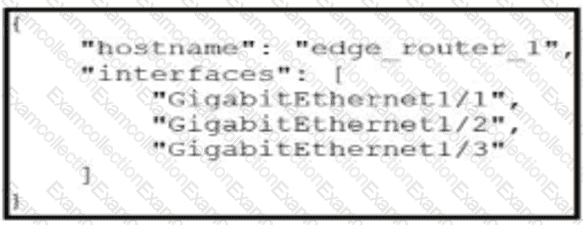
Which exhibit displays a valid JSON file?
A)
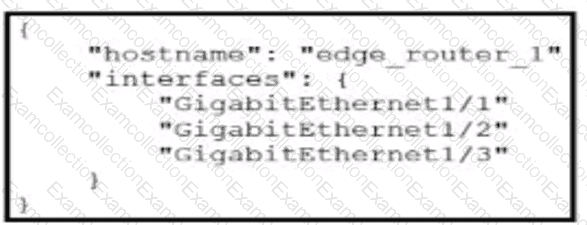
B)
C)
D)
In Cisco CatalystCenter(formerly DNA Center) Inventory, the Software Version of a networkdevice displays a status of OUTDATED. What does It me?
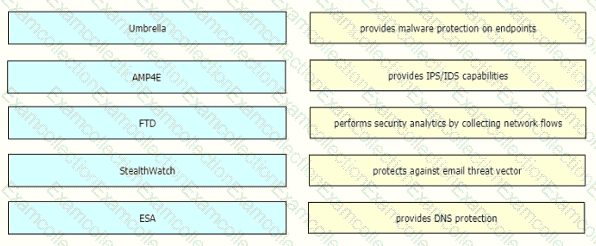
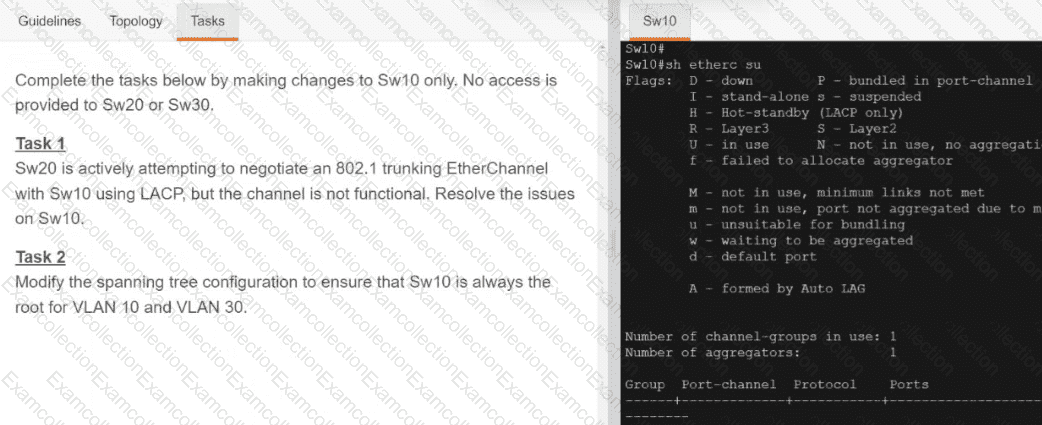
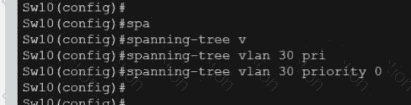
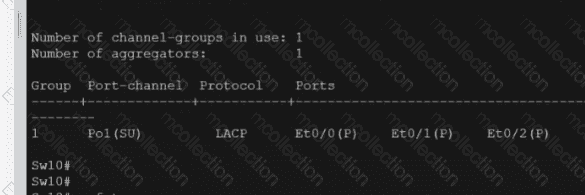
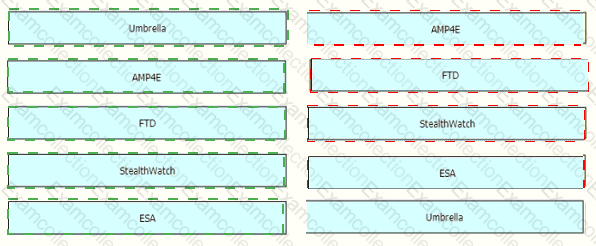
Drag and drop the threat defense solutions from the left onto their descriptions on the right.