CompTIA CAS-004 - CompTIA SecurityX Certification Exam
A security engineer is implementing a server-side TLS configuration that provides forward secrecy and authenticated encryption with associated data. Which of the following algorithms, when combined into a cipher suite, will meet these requirements? (Choose three.)
A security manager wants to transition the organization to a zero trust architecture. To meet this requirement, the security manager has instructed administrators to remove trusted zones, role-based access, and one-time authentication. Which of the following will need to be implemented to achieve this objective? (Select THREE).
A company is deploying multiple VPNs to support supplier connections into its extranet applications. The network security standard requires:
• All remote devices to have up-to-date antivirus
• An up-to-date and patched OS
Which of the following technologies should the company deploy to meet its security objectives? (Select TWO)_
An engineering team has deployed a new VPN service that requires client certificates to be used in order to successfully connect. On iOS devices, however, the following error occurs after importing the .p12 certificate file:
mbedTLS: ca certificate undefined
Which of the following is the root cause of this issue?
A bank hired a security architect to improve its security measures against the latest threats The solution must meet the following requirements
• Recognize and block fake websites
• Decrypt and scan encrypted traffic on standard and non-standard ports
• Use multiple engines for detection and prevention
• Have central reporting
Which of the following is the BEST solution the security architect can propose?
A security officer is requiring all personnel working on a special project to obtain a security clearance requisite with the level of all information being accessed Data on this network must be protected at the same level of each clearance holder The need to know must be vended by the data owner Which of the following should the security officer do to meet these requirements?
A security review of the architecture for an application migration was recently completed. The following observations were made:
• External inbound access is blocked.
• A large amount of storage is available.
• Memory and CPU usage are low.
• The load balancer has only a single server assigned.
• Multiple APIs are integrated.
Which of the following needs to be addressed?
Several unlabeled documents in a cloud document repository contain cardholder information. Which of the following configuration changes should be made to the DLP system to correctly label these documents in the future?
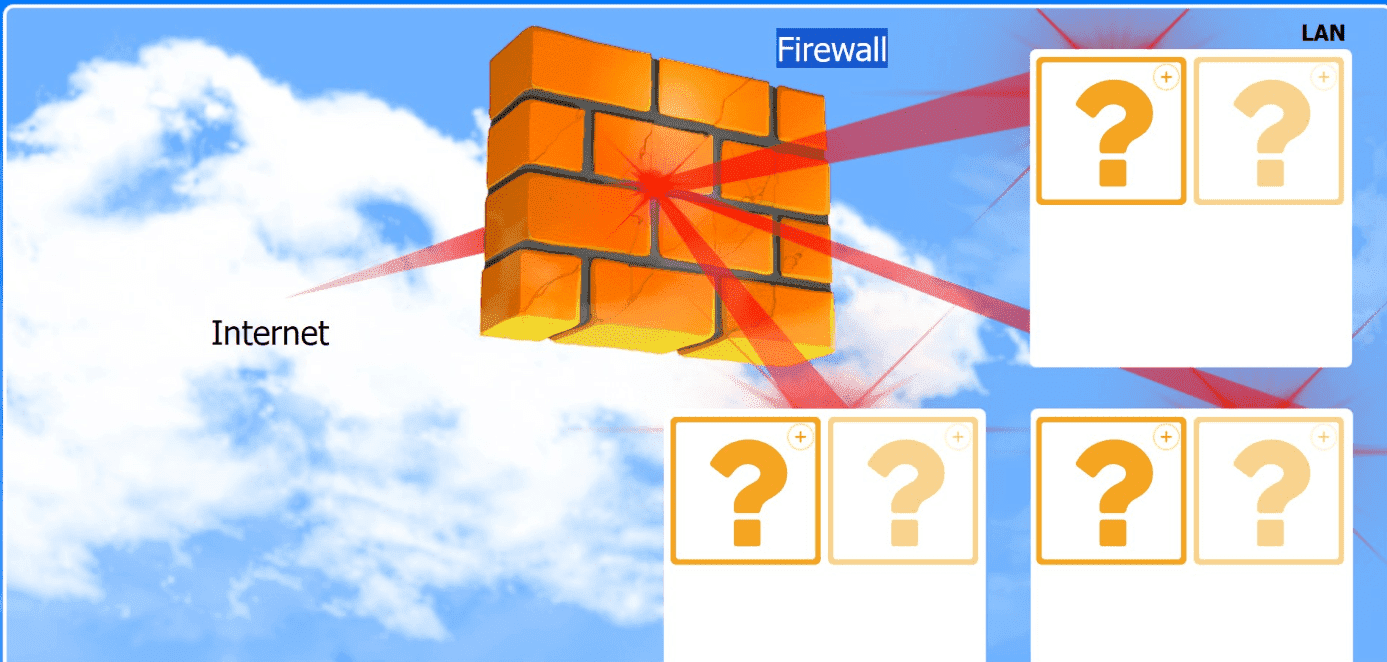
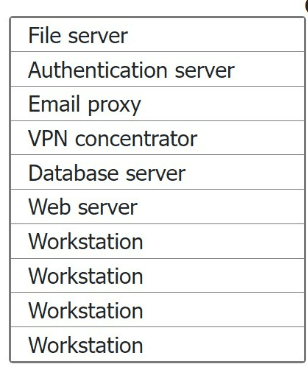
You are an information security analyst tasked to provide feedback and remediation
guidance to an organization that is working to comply with a prescriptive framework.
The framework includes the following controls related to network design:
. Network hosts must be segmented into security domains.
. A screened subnet must be used for all externally available assets.
. A shared services zone must be present for internal servers and should not contain workstations.
INSTRUCTIONS
Based on the stated requirements, place each resource in the appropriate network location. All resources must be used, and all network zones will be filled.
A company's software developers have indicated that the security team takes too long to perform application security tasks. A security analyst plans to improve the situation by implementing security into the SDLC. The developers have the following requirements:
1. The solution must be able to initiate SQL injection and reflected XSS attacks.
2. The solution must ensure the application is not susceptible to memory leaks.
Which of the following should be implemented to meet these requirements? (Select two).
A security analyst and a DevOps engineer are working together to address configuration drifts in highly scalable systems that are leading to increased vulnerability findings. Which of the following recommendations would be best to eliminate this issue?
A company is migrating its data center to the cloud. Some hosts had been previously isolated, but a risk assessment convinced the engineering team to reintegrate the systems. Because the systems were isolated, the risk associated with vulnerabilities was low. Which of the following should the security team recommend be performed before migrating these servers to the cloud?
An multinational organization was hacked, and the incident response team's timely action prevented a major disaster Following the event, the team created an after action report. Which of the following is the primary goal of an after action review?
A software developer has been tasked with creating a unique threat detection mechanism that is based on machine learning. The information system for which the tool is being developed is on a rapid CI/CD pipeline, and the tool developer is considered a supplier to the process. Which of the following presents the most risk to the development life cycle and lo the ability to deliver the security tool on time?
A company's BIA indicates that any loss of more than one hour of data would be catastrophic to the business. Which of the following must be in place to meet this requirement?



