CompTIA CS0-003 - CompTIA CyberSecurity Analyst CySA+ Certification Exam
A Chief Information Security Officer (CISO) has determined through lessons learned and an associated after-action report that staff members who use legacy applications do not adequately understand how to differentiate between non-malicious emails and phishing emails. Which of the following should the CISO include in an action plan to remediate this issue?
A user downloads software that contains malware onto a computer that eventually infects numerous other systems. Which of the following has the user become?
Which of the following would a security analyst most likely use to compare TTPs between different known adversaries of an organization?
A security analyst has found a moderate-risk item in an organization ' s point-of-sale application. The organization is currently in a change freeze window and has decided that the risk is not high enough to correct at this time. Which of the following inhibitors to remediation does this scenario illustrate?
An attacker recently gained unauthorized access to a financial institution ' s database, which contains confidential information. The attacker exfiltrated a large amount of data before being detected and blocked. A security analyst needs to complete a root cause analysis to determine how the attacker was able to gain access. Which of the following should the analyst perform first?
A company patches its servers using automation software. Remote SSH or RDP connections are allowed to the servers only from the service account used by the automation software. All servers are in an internal subnet without direct access to or from the internet. An analyst reviews the following vulnerability summary:
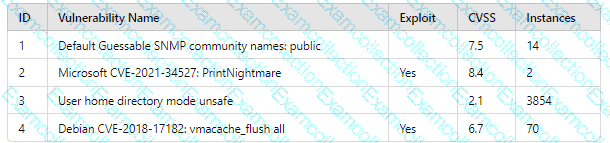
Which of the following vulnerability IDs should the analyst address first?
A manufacturer has hired a third-party consultant to assess the security of an OT network that includes both fragile and legacy equipment Which of the following must be considered to ensure the consultant does no harm to operations?
A cybersecurity team has witnessed numerous vulnerability events recently that have affected operating systems. The team decides to implement host-based IPS, firewalls, and two-factor authentication. Which of the following
does this most likely describe?
During a routine review of DNS logs, a security analyst observes that Host X has been making frequent DNS requests to domains with random alphanumeric strings, such as ajd8ekthj.xyz. IPS anomaly rules are blocking these domains. This behavior started shortly after a new software installation on the host. Which of the following should the analyst do first to determine whether Host X has been compromised?
An organization is conducting a pilot deployment of an e-commerce application. The application ' s source code is not available. Which of the following strategies should an analyst recommend to evaluate the security of the software?



