CompTIA CS0-003 - CompTIA CyberSecurity Analyst CySA+ Certification Exam
After completing a review of network activity. the threat hunting team discovers a device on the network that sends an outbound email via a mail client to a non-company email address daily
at 10:00 p.m. Which of the following is potentially occurring?
Which of the following threat actors is most likely to target a company due to its questionable environmental policies?
The SOC received a threat intelligence notification indicating that an employee ' s credentials were found on the dark web. The user ' s web and log-in activities were reviewed for malicious or anomalous connections, data uploads/downloads, and exploits. A review of the controls confirmed multifactor
authentication was enabled. Which of the following should be done first to mitigate impact to the business networks and assets?
Which of the following is a nation-state actor least likely to be concerned with?
While reviewing the web server logs, a security analyst notices the following snippet:
.. \ .. / .. \ .. /boot.ini
Which of the following Is belng attempted?
An organization has a critical financial application hosted online that does not allow event logging to send to the corporate SIEM. Which of the following is the best option for the security analyst to configure to improve the efficiency of security operations?
Which of the following phases of the Cyber Kill Chain involves the adversary attempting to establish communication with a successfully exploited target?
A penetration tester is conducting a test on an organization ' s software development website. The penetration tester sends the following request to the web interface:
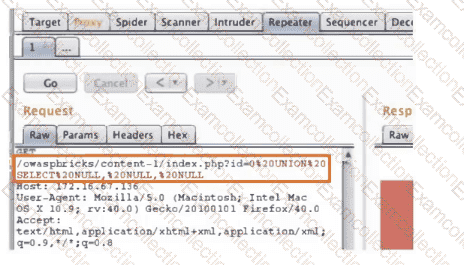
Which of the following exploits is most likely being attempted?
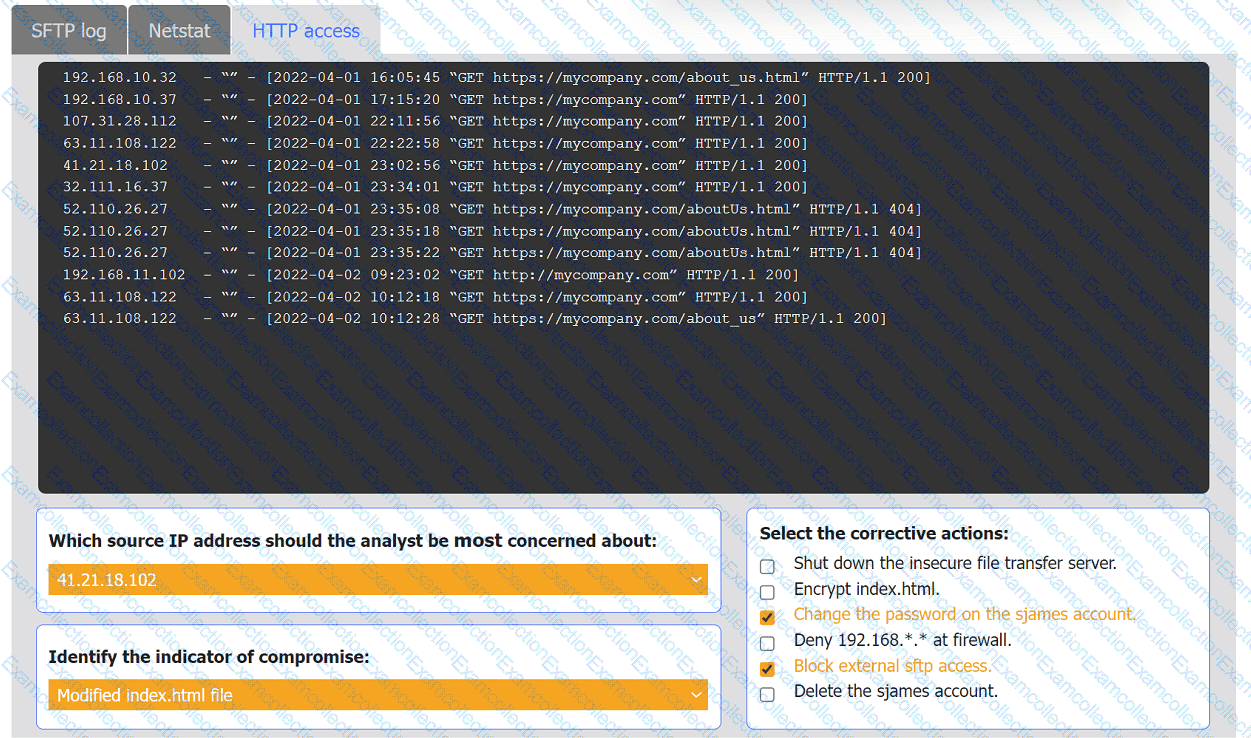
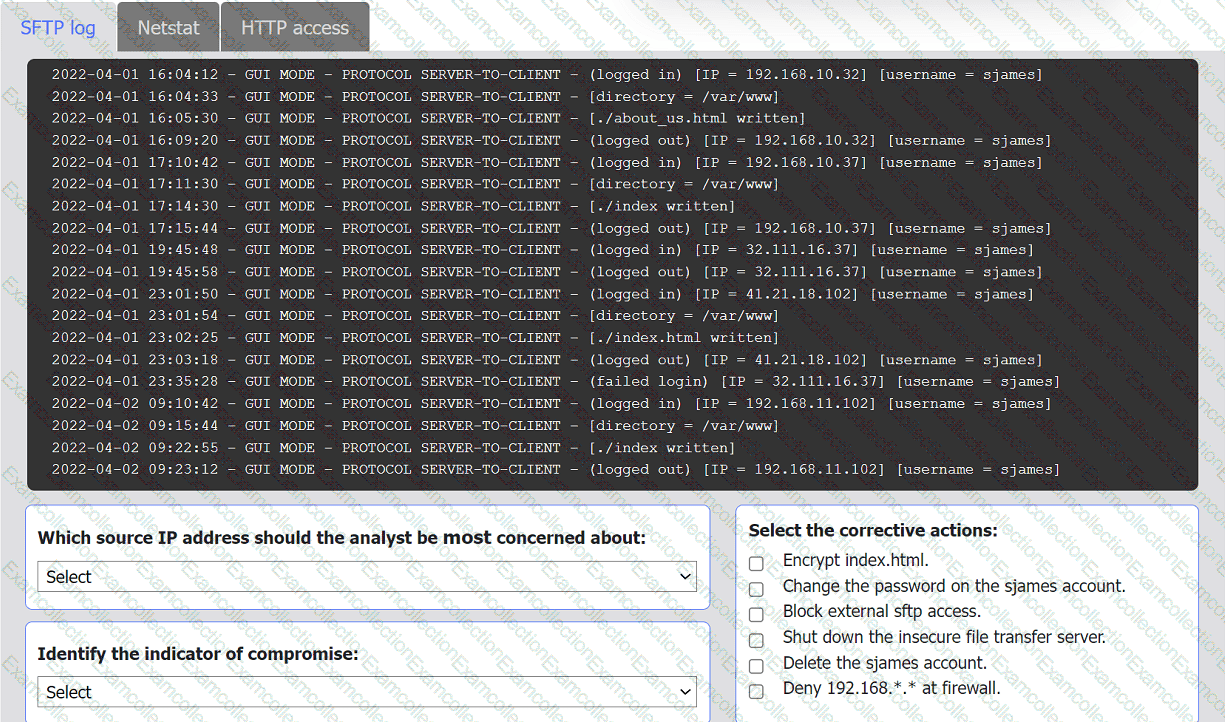
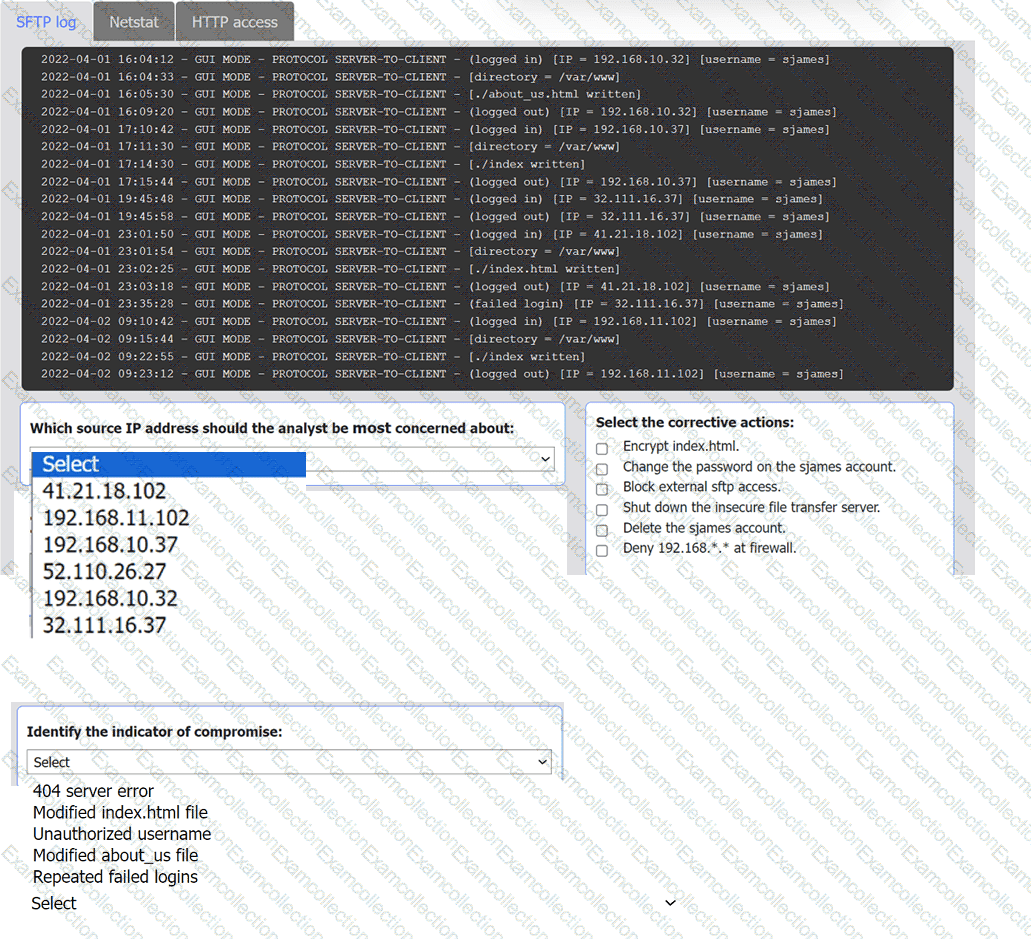
An organization ' s website was maliciously altered.
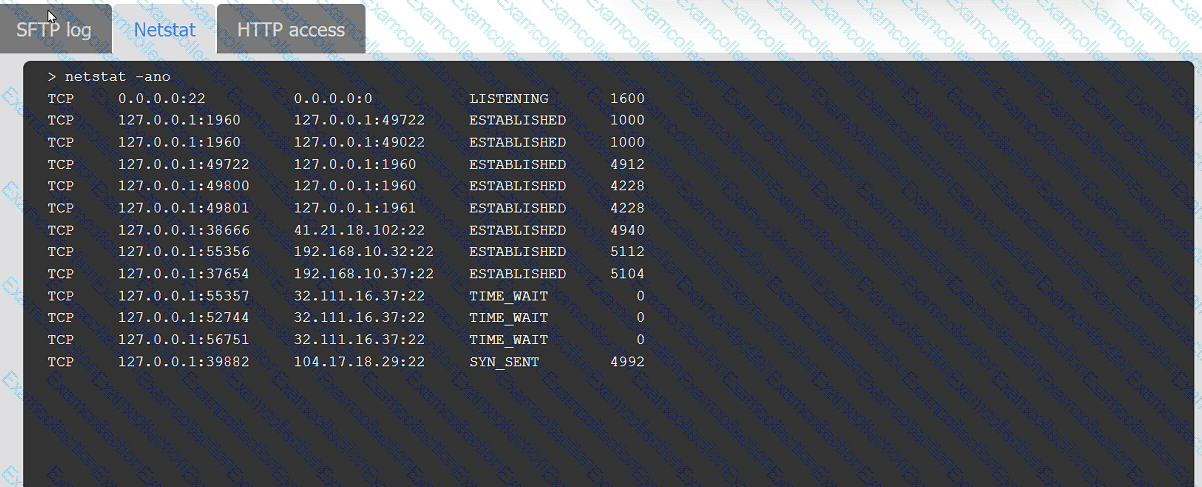
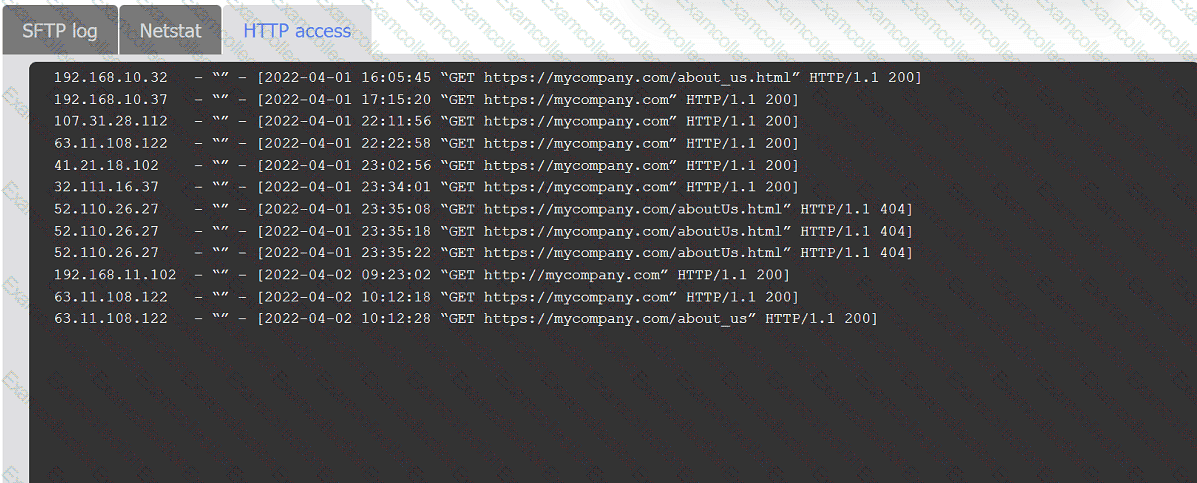
INSTRUCTIONS
Review information in each tab to select the source IP the analyst should be concerned
about, the indicator of compromise, and the two appropriate corrective actions.
Security analysts review logs on multiple servers on a daily basis. Which of the following implementations will give the best central visibility into the events occurring throughout the corporate environment without logging in to the servers individually?