CompTIA CS0-003 - CompTIA CyberSecurity Analyst CySA+ Certification Exam
A SOC manager is establishing a reporting process to manage vulnerabilities. Which of the following would be the best solution to identify potential loss incurred by an issue?
A vulnerability scan shows the following vulnerabilities in the environment:
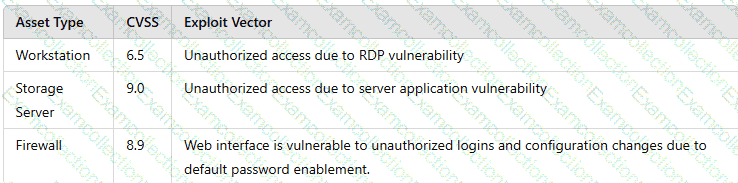
At the same time, the following security advisory was released:
" A zero-day vulnerability with a CVSS score of 10 may be affecting your web server. The vendor is working on a patch or workaround. "
Which of the following actions should the security analyst take first?
A technician identifies a vulnerability on a server and applies a software patch. Which of the following should be the next step in the remediation process?
An organization wants to establish a disaster recovery plan for critical applications that are hosted on premises. Which of the following is the first step to prepare for supporting this new requirement?
The analyst reviews the following endpoint log entry:
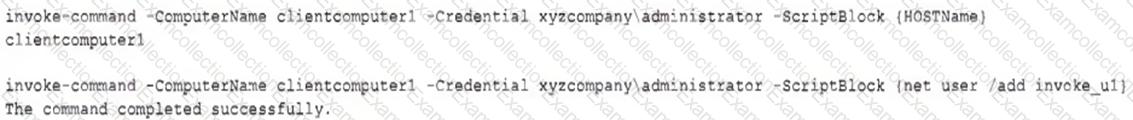
Which of the following has occurred?
Several reports with sensitive information are being disclosed via file sharing services. The company would like to improve its security posture against this threat. Which of the following security controls would best support the company in this scenario?
An organization is planning to adopt a zero-trust architecture. Which of the following is most aligned with this approach?
While reviewing web server logs, a security analyst discovers the following suspicious line:
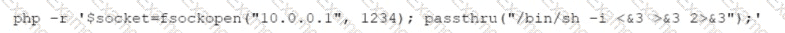
Which of the following is being attempted?
An incident responder was able to recover a binary file through the network traffic. The binary file was also found in some machines with anomalous behavior. Which of the following processes most likely can be performed to understand the purpose of the binary file?
Which of the following is the most important reason for an incident response team to develop a formal incident declaration?



