Fortinet NSE4_FGT_AD-7.6 - Fortinet NSE 4 - FortiOS 7.6 Administrator
An administrator wants to form an HA cluster using the FGCP protocol. Which two requirements must the administrator ensure both members fulfill? (Choose two answers)
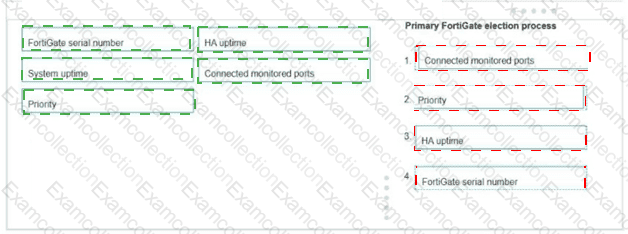
An administrator wants to form an HA cluster using the FGCP protocol. Both FortiGate devices are configured with the set override enable command. Arrange the criteria in the order in which the FGCP protocol uses them to elect the primary FortiGate. Select the criteria in the left column, hold and drag it to a blank position in the column on the right. Place the four correct steps in order, placing the first step in the first position. Once you place a step, you can move it again if you want to change your answer before moving to the next question. You need to drop four criteria in the work area. Select and drag the screen divider to change the viewable area of the source and work areas. (Choose four answers)
An administrator wants to address shadow IT visibility challenges and prevent users from sending sensitive files outside the organization without proper approval. Which FortiSASE method should the administrator implement to achieve these goals? (Choose one answer)
A network administrator has enabled full SSL inspection and web filtering on FortiGate. When visiting any HTTPS websites, the browser reports certificate warning errors. When visiting HTTP websites, the browser does not report errors.
What is the reason for the certificate warning errors?
Refer to the exhibit.
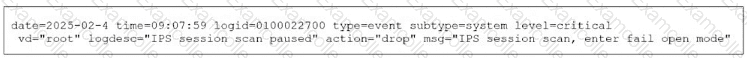
What can you conclude from the log shown in the exhibit?
Refer to the exhibit.
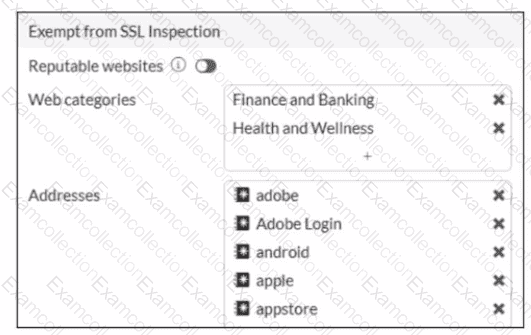
The predefined deep-inspection and custom-deep-inspection profiles exclude some web categories from SSL inspection, as shown in the exhibit For which two reasons are these web categories exempted? (Choose two.)
Refer to the exhibits.
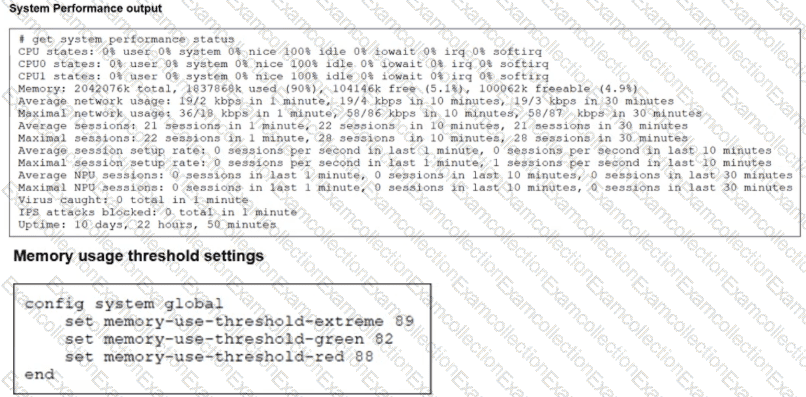
The exhibits show the system performance output and default configuration of high memory usage thresholds on a FortiGate device.
Based on the system performance output, what are the two possible outcomes? (Choose two.)
An administrator has configured the following settings.
config system settings
set ses-denied-traffic enable
end
config system global
set block-session-timer 30
end
What are the two results of this configuration? (Choose two.)
A network administrator is configuring an IPsec VPN tunnel for a sales employee travelling abroad.
Which VPN Wizard template must the administrator apply?
How does FortiExtender connect to FortiSASE in a site-based, remote internet access method?