Fortinet NSE4_FGT_AD-7.6 - Fortinet NSE 4 - FortiOS 7.6 Administrator
Which three statements about SD-WAN performance SLAs are true? (Choose three.)
Refer to the exhibit.
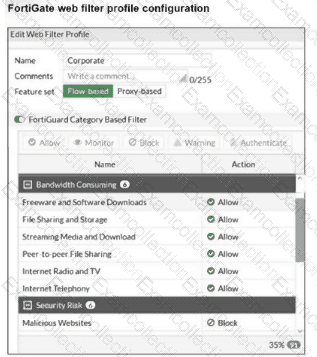
The exhibit shows the FortiGuard Category Based Filter section of a corporate web filter profile. An administrator must block access to download.com, which belongs to the Freeware and Software Downloads category. The administrator must also allow other websites in the same category. What are two solutions for satisfying the requirement? (Choose two answers)
Which two statements about equal-cost multi-path (ECMP) configuration on FortiGate are true? (Choose two answers)
You have implemented the application sensor and the corresponding firewall policy as shown in the exhibits.
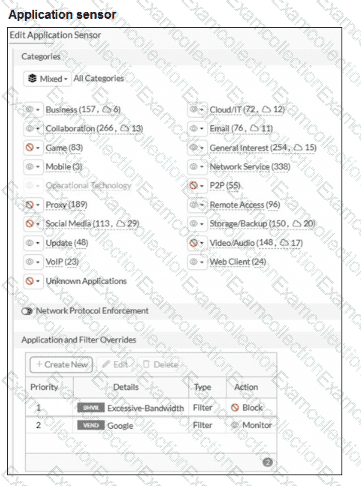
You cannot access any of the Google applications, but you are able to access www.fortinet.com .
What would you do to resolve this issue?
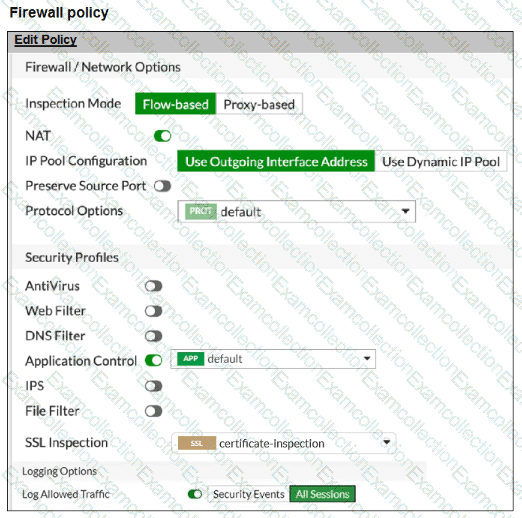
Refer to the exhibit.
A network administrator is troubleshooting an IPsec tunnel between two FortiGate devices. The administrator has determined that phase 1 status is up, but phase 2 fails to come up.
Based on the phase 2 configuration shown in the exhibit, which two configuration changes will bring phase 2 up? (Choose two.)
A network administrator enabled antivirus and selected an SSL inspection profile on a firewall policy. When downloading an EICAR test file through HTTP, FortiGate detects the virus and blocks the file. When downloading the same file through HTTPS, FortiGate does not detect the virus and does not block the file, allowing it to be downloaded. The administrator confirms that the traffic matches the configured firewall policy. What are two reasons for the failed virus detection by FortiGate? (Choose two answers)
Refer to the exhibit.
A routing table is shown
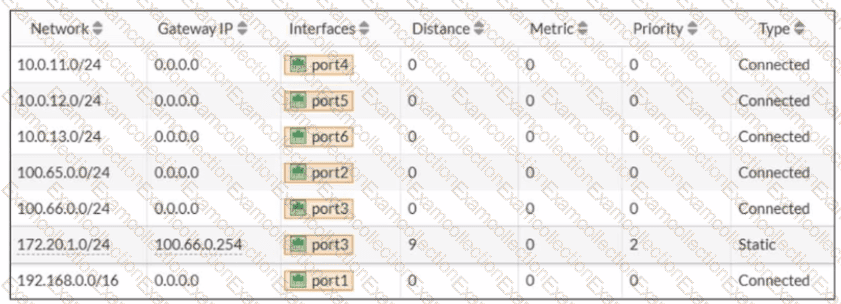
An administrator wants to create a new static route so the traffic to the subnet 172.20.1.0/24 is routed through port2 only. What are the two criteria that the administrator can use to achieve this objective? (Choose two.)
Refer to the exhibit.
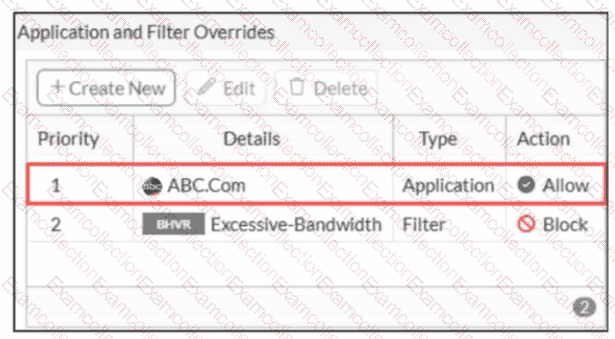
An administrator has configured an Application Overrides for the ABC.Com application signature and set the Action to Allow This application control profile is then applied to a firewall policy that is scanning all outbound traffic. Logging is enabled in the firewall policy. To test the configuration, the administrator accessed the ABC.Com web site several times.
Why are there no logs generated under security logs for ABC.Com?
What are two features of collector agent advanced mode? (Choose two.)
Refer to the exhibit, which shows a partial configuration from the remote authentication server.

Why does the FortiGate administrator need this configuration? (Choose one answer)



